How to Install Symantec Endpoint Protection Client on Mac
- CLOUD SOLUTIONS
- Inventory management
- Network inventory
- Running tasks
Running tasks
Running tasks on endpoints
From the Network page, you can remotely run a number of administrative tasks on endpoints.
This is what you can do:
-
Scan
-
Scan for IOC
-
Risk scan
-
Patch tasks
-
Exchange scan
-
Install
-
Uninstall client
-
Update client
-
Reconfigure client
-
Repair client
-
Restart machine
-
Network discovery
-
Update Security Server
You can choose to create tasks individually for each endpoint or for groups of endpoints. For example, you can remotely install the security agent on a group of unmanaged endpoints. At a later time, you can create a scan task for a certain endpoint from the same group.
For each endpoint, you can only run compatible tasks. For example, if you select an unmanaged endpoint, you can only choose to install the security agent, all the other tasks being disabled.
For a group, the selected task will be created only for compatible endpoints. If none of the endpoints in the group is compatible with the selected task, you will be notified that the task could not be created.
Once created, the task will start running immediately on the online endpoints. If an endpoint is offline, the task will run as soon as it gets back online.
You can view and manage the task in the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Scan
To remotely run a scan task on one or several endpoints:
-
Go to the Network page.
-
Select the container that you want from the left-side pane. All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check boxes of endpoints or groups you want to scan.
-
Click the
 Tasks button at the upper side of the table and choose Scan .
Tasks button at the upper side of the table and choose Scan .A configuration window will appear.
-
Configure the scan options:
-
In the General tab, you can choose the type of scan and you can enter a name for the scan task.
The scan task name is intended to help you easily identify the current scan in the Tasks page.

Select the type of scan from the Type menu:
-
Quick scan uses in-the-cloud scanning to detect malware running in the system. This type of scan is preconfigured to allow scanning only critical Windows and Linux system locations. Running a Quick Scan usually takes less than a minute and uses a fraction of the system resources needed by a regular virus scan.
When malware or rootkits are found, Bitdefender automatically proceeds with disinfection. If, for any reason, the file cannot be disinfected, then it is moved to quarantine. This type of scanning ignores suspicious files.
-
Full scan checks the entire system for all types of malware threatening its security, such as viruses, spyware, adware, rootkits and others.
Bitdefender automatically tries to disinfect files detected with malware. In case malware cannot be removed, it is contained in quarantine, where it cannot do any harm. Suspicious files are being ignored. If you want to take action on suspicious files as well, or if you want other default actions for infected files, then choose to run a Custom Scan.
-
Memory scan checks the programs running in the endpoint's memory.
-
Network scan is a type of custom scan, allowing to scan network drives using the Bitdefender security agent installed on the target endpoint.
For the network scan task to work:
-
You need to assign the task to one single endpoint in your network.
-
You need to enter the credentials of a user account with read/write permissions on the target network drives, for the security agent to be able to access and take actions on these network drives. The required credentials can be configured in the Target tab of the tasks window.
-
-
Custom scan allows you to choose the locations to be scanned and to configure the scan options.
For memory, network and custom scans, you have also these options:
-
Run the task with low priority . Select this check box to decrease the priority of the scan process and allow other programs to run faster. This will increase the time needed for the scan process to finish.
Note
This option applies only to Bitdefender Endpoint Security Tools.
-
Shut down computer when scan is finished . Select this check box to turn off your machine if you do not intend to use it for a while.
Note
This option applies to Bitdefender Endpoint Security Tools and Endpoint Security for Mac.
Note
These two options apply only to Bitdefender Endpoint Security Tools.
For custom scans, configure the following settings:
-
Go to the Options tab to set the scan options.
Click the security level that best suits your needs (Aggressive, Normal or Permissive).
Use the description on the right-side of the scale to guide your choice.
Based on the selected profile, the scan options in the Settings section are automatically configured. However, if you want to, you can configure them in detail. To do that, select the Custom check box and then expand the Settings section.

The following options are available:
-
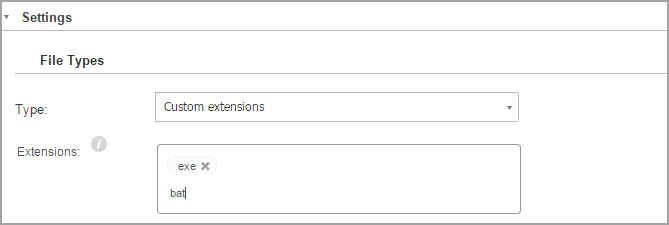
File types
Use these options to specify which types of files you want to be scanned.
You can set the security agent to scan all files (regardless of their file extension), application files only or specific file extensions you consider to be dangerous.
Scanning all files provides best protection, while scanning applications only can be used to perform a quicker scan.
Note
Application files are far more vulnerable to malware attacks than other types of files.
For more information, refer to Application file types.
If you want only specific extensions to be scanned, choose Custom extensions from the menu and then enter the extensions in the edit field, pressing
Enterafter each extension.Important
Bitdefender security agents installed on Windows and Linux operating systems scan most of the .ISO formats, but does not take any action on them.
-
Archives
Archives containing infected files are not an immediate threat to system security.
The malware can affect the system only if the infected file is extracted from the archive and executed without having real-time protection enabled.
However, it is recommended to scan archives in order to detect and remove any potential threat, even if it is not an immediate threat.
Important
Scanning archived files increases the overall scanning time and requires more system resources.
-
Scan inside archives
Select this option if you want to check archived files for malware.
If you decide on using this option, you can configure the following optimization options:
-
Limit archive size to (MB)
You can set a maximum accepted size limit of archives to be scanned.
Select the corresponding check box and type the maximum archive size (in MB).
-
Maximum archive depth (levels)
Select the corresponding check box and choose the maximum archive depth from the menu.
For best performance choose the lowest value, for maximum protection choose the highest value.
-
-
Scan email archives
Select this option if you want to enable scanning of email message files and email databases, including file formats such as .eml, .msg, .pst, .dbx, .mbx, .tbb and others.
Important
Email archive scanning is resource intensive and can impact system performance.
-
-
Miscellaneous
Select the corresponding check boxes to enable the desired scan options.
-
Scan boot sectors
Scans the system's boot sector.
This sector of the hard disk contains the necessary computer code to start the boot process.
When a virus infects the boot sector, the drive may become inaccessible and you may not be able to start your system and access your data.
-
Scan registry
Select this option to scan registry keys.
Windows Registry is a database that stores configuration settings and options for the Windows operating system components, as well as for installed applications.
-
Scan for rootkits
Select this option to scan for glossary.rootkit rootkits and objects hidden using such software.
-
Scan for keyloggers
Select this option to scan for glossary.keylogger keylogger software.
-
Scan network shares
This option scans mounted network drives.
For quick scans, this option is deactivated by default. For full scans, it is activated by default. For custom scans, if you set the security level to Aggressive/Normal , the Scan network shares option is automatically enabled. If you set the security level to Permissive , the Scan network shares option is automatically disabled.
-
Scan memory
Select this option to scan programs running in the system's memory.
-
Scan cookies
Select this option to scan the cookies stored by browsers on the computer.
-
Scan only new and changed files
By scanning only new and changed files, you may greatly improve overall system responsiveness with a minimum trade-off in security.
-
Scan for Potentially Unwanted Applications (PUA)
A Potentially Unwanted Application (PUA) is a program that may be unwanted on the PC and sometimes comes bundled with freeware software. Such programs can be installed without the user's consent (also called adware) or will be included by default in the express installation kit (ad-supported). Potential effects of these programs include the display of pop-ups, installing unwanted toolbars in the default browser or running several processes in the background and slowing down the PC performance.
-
Scan detachable volumes
-
-
Actions
Depending on the type of detected file, the following actions are taken automatically:
-
When an infected file is found
Bitdefender detects files as infected through various advanced mechanisms, which include malware signatures, machine learning and artificial intelligence (AI) based technologies.
The Bitdefender security agent can normally remove the malware code from an infected file and reconstruct the original file. This operation is known as disinfection.
By default, if an infected file is detected, the Bitdefender security agent will automatically attempt to disinfect it.
If disinfection fails, the file is moved to quarantine in order to contain the infection.
Important
For particular types of malware, disinfection is not possible because the detected file is entirely malicious. In such cases, the infected file is deleted from the disk.
-
When a suspect file is found
Files are detected as suspicious by the heuristic analysis and other Bitdefender technologies.
These provide a high detection rate, but the users must be aware of certain false positives (clean files detected as suspicious) in some cases.
Suspect files cannot be disinfected, because no disinfection routine is available.
Scan tasks are configured by default to ignore suspect files.
You may want to change the default action in order to move suspect files to quarantine.
Quarantined files are sent for analysis to Bitdefender Labs on a regular basis.
If malware presence is confirmed, a signature is released to allow removing the malware.
-
When a rootkit is found
Rootkits represent specialized software used to hide files from the operating system.
Though not malicious in nature, rootkits are often used to hide malware or to conceal the presence of an intruder into the system.
Detected rootkits and hidden files are ignored by default.
Though not recommended, you can change the default actions.
You can specify a second action to be taken if the first one fails and different actions for each category.
Choose from the corresponding menus the first and the second action to be taken on each type of detected file.
The following actions are available:
-
Disinfect
Remove the malware code from infected files.
It is recommended to always keep this as the first action to be taken on infected files.
-
Move files to quarantine
Move detected files from their current location to the quarantine folder.
Quarantined files cannot be executed or opened; therefore, the risk of getting infected disappears.
You can manage quarantine files from the quarantine Quarantine page of the console.
-
Delete
Delete detected files from the disk, without any warning.
It is advisable to avoid using this action.
-
Ignore
No action will be taken on detected files. These files will only appear in the scan log.
-
-
-
Go to Target tab to configure the locations you want to be scanned on the target endpoints.
In the Scan target section you can add a new file or folder to be scanned:
-
Choose a predefined location from the drop-down menu or enter the Specific paths you want to scan.
-
Specify the path to the object to be scanned in the edit field.
-
If you have chosen a predefined location, complete the path as needed.
For example, to scan the entire
Program Filesfolder, it suffices to select the corresponding predefined location from the drop-down menu.To scan a specific folder from
Program Files, you must complete the path by adding a backslash (\) and the folder name. -
If you have chosen Specific paths , enter the full path to the object to be scanned.
It is advisable to use system variables (where appropriate) to make sure the path is valid on all target computers. For more information regarding system variables, refer to appendices.variables.
-
-
Click the corresponding add_inline.png Add button.
To edit an existing location, click it.
To remove a location from the list, click the corresponding elete_inline.png Delete button.
For network scan tasks, you need to enter the credentials of a user account with read/write permissions on the target network drives, for the security agent to be able to access and take actions on these network drives.
Click the Exclusions section if you want to define target exclusions.
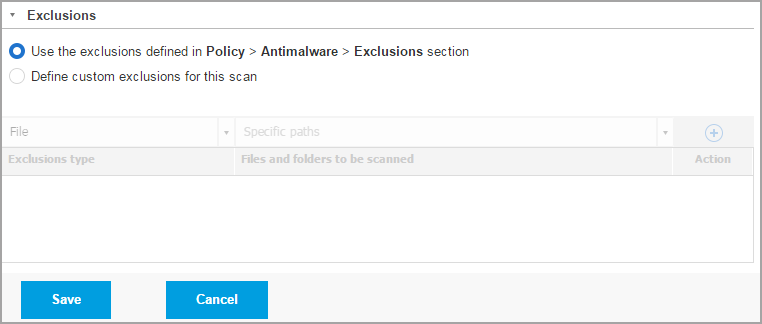
You can either use the exclusions defined by policy or define explicit exclusions for the current scan task.
For more details regarding exclusions, refer to Settings.
-
-
-
-
Click Save to create the scan task. A confirmation message will appear.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Note
To schedule a scan task, go to the Policies page, select the policy assigned to the computers you are interested in, and add a scan task in the Antimalware > On-demand section. For more information, refer to On-demand.
Scan for IOC
At any time, you can choose to run on-demand scanning for known Indicators of Compromise (IOC) on selected endpoints.
Important
This task is only available for plans that include the EDR feature.
-
Go to the Network page.
-
Browse the containers and select the endpoints you want to scan.
-
Click the
 Tasks button and choose Scan for IOC.
Tasks button and choose Scan for IOC.A configuration page will appear, where you need to select the type of indicators taken into account for IOC scanning.

Important
You must select at least one type of Indicator of Compromise to create a valid task.
-
Select one or more IOC types you want to take into account for scanning and write the known IOC name in the newly added field.

You can select from the following types:
-
MD5
-
SHA1
-
SHA256
-
SHA512
-
File names
-
Process names
-
Registry values
-
Registry keys
Note
Content added inside each field must be valid. You will be prompted a warning sign and message if otherwise.
-
-
Click Save to create and run the Scan for IOC task.
A confirmation message will appear.
You can check the task's progress in the Network > Tasks page.

-
Once the task has finished successfully you can click the
 Reports button to read the generated report and assess the impact of the scanned-for IOC.
Reports button to read the generated report and assess the impact of the scanned-for IOC.
Valid file extensions for IOCs added to the task include: exe, dll, com, scr, jar, msi, msc, bat, ps1, vbs, vbe, js, jse, wsf, wsh, psc1, lnk, doc, docx, docm, xls, xlsx, xlsm, ppt, pptx, pptm, eml, rtf, pdf, html, ppsx, pps, ppsm, pot, potx, potm, ocx, sys, fnr, fne, and pif.
The Scan for IOC task will scan the following locations.
-
%Windows%\System32\Drivers -
%Windows%\System32\WindowsPowerShell\v1.0 -
%Windows%\system32\config\systemprofile\AppData -
%Windows%\System32\Tasks -
%Windows%\System32\wbem -
%Windows%\SysWOW64\WindowsPowerShell\v1.0 -
%Windows%\SysWOW64\config\systemprofile\AppData -
%Windows%\SysWOW64\sysprep -
%Windows%\Scripts -
%Windows%\System -
%Windows%\Web -
%Users%
Important
The Scan for IOC tasks will not run / will fail on endpoints in the following situations:
-
The endpoint does not have a Windows operating system.
-
The endpoint's Bitdefender agent license is invalid.
-
The EDR module is not installed in the security agent installed on the target endpoints.
-
More than 100 Scan for IOC tasks are currently in queue.
-
Invalid data is entered by user in the Scan for IOC task configuration page.
Risk scan
You can anytime choose to run on demand risk scan tasks on selected endpoints, as follows:
-
Go to the Network page.
-
Browse the containers from the left-side pane and select the endpoints you want to scan.
-
Click the
 Tasks button at the upper side of the table and choose Risk scan .
Tasks button at the upper side of the table and choose Risk scan .A configuration page will appear, where you need to select the indicators taken into account for risk scanning.
Note
An Indicator of Risk refers to a registry key value or data of a specific system setting.
-
Select the indicators of risk you want to take into account for scanning.
Indicators of risk are grouped by the following attributes:
-
Category (Network, Operating System)
-
Severity (Misconfiguration, Microsoft Security Baseline)
By default, only a certain number of indicators are selected. You may need to review the list of indicators you want to include for scanning.
You can also use the search bar to find specific indicators. Note that risk indicator names include terms from local or group policy names. To view the full list of indicators and their description, refer to GravityZone Indicators of Risk.
-
-
Click Save to create the scan task. A confirmation message will appear.
Important
The Risk scan tasks will not run / will fail on endpoints in the following situations:
-
The endpoint does not have a Windows operating system.
-
The endpoint's Bitdefender agent license is invalid.
-
The policy applied to endpoint has the Risk Management module disabled.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Exchange scan
You can remotely scan the database of an Exchange Server by running an Exchange scan task.
To be able to scan the Exchange database, you must enable on-demand scanning by providing the credentials of an Exchange administrator. For more information, refer to Exchange Store Scanning.
To scan an Exchange Server database:
-
Go to the Network page.
-
From the left-side pane, select the group containing the target Exchange Server. You can find the server displayed in the right-side pane.
Note
Optionally, you can apply filters to quickly find the target server:
-
Click the Filters menu and select the following options: Managed (Exchange Servers) from the Security tab and All items recursively from the Depth tab.
-
Enter the server's hostname or IP in the fields from the corresponding column headers.
-
-
Select the check box of the Exchange Server whose database you want to scan.
-
Click the Tasks button at the upper side of the table and choose Exchange scan . A configuration window will appear.
-
Configure the scan options:
-
General. Enter a suggestive name for the task.
For large databases, the scan task may take a long time and may impact the server performance. In such cases, select the check box Stop scan if it takes longer than and choose a convenient time interval from the corresponding menus.
-
policies.computers.exchange.antimalware.store.settings.target
-
policies.computers.exchange.antimalware.transport.rules.settings
-
policies.computers.exchange.antimalware.transport.rules.actions
-
-
Click Save to create the scan task. A confirmation message will appear.
-
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Install
To protect your endpoints with the Bitdefender security agent, you must install it on each of them.
Once you have installed a Relay agent, it will automatically detect unprotected endpoints in the same network.
The Bitdefender protection can then be installed on endpoints remotely from Control Center.
Remote installation is performed in the background, without the user knowing about it.
Warning
Before installation, be sure to uninstall existing antimalware and firewall software from computers.
Installing the Bitdefender protection over existing security software may affect their operation and cause major problems with the system.
Windows Defender and Windows Firewall will be turned off automatically when installation starts.
If you want to deploy the security agent on a computer with Bitdefender Antivirus for Mac 5.X, you first must remove the latter manually. For the guiding steps, refer to Deploy Endpoint Security for Mac on a machine with Bitdefender Antivirus for Mac 5.X.
When deploying the agent through a Linux Relay, the following conditions must be met:
-
The Relay endpoint must have installed the Samba package (
smbclient) version 4.1.0 or above and thenetbinary/command to deploy Windows agents.The
netbinary/command is usually delivered with the samba-client and / or samba-common packages. On some Linux distributions (such as CentOS 7.4), thenetcommand is only being installed when installing the full Samba suite (Common + Client + Server). Make sure that your Relay endpoint has thenetcommand available. -
Target Windows endpoints must have Administrative Share and Network Share enabled.
-
Target Linux and Mac endpoints must have SSH enabled and firewall disabled.
To run a remote installation task:
-
Connect and log in to Control Center.
-
Go to the Network page.
-
Select the desired group from the left-side pane.
The entities contained in the selected group are displayed in the right-side pane table.
Optionally, you can apply filters to display unmanaged endpoints only. Click the Filters menu and select the following options: Unmanaged from the Security tab and All items recursively from the Depth tab.
When working with EC2 instances, you can also add the EC2 Instances option in the Type tab, while applying all the other above mentioned criteria.
-
Select the entities (endpoints or groups of endpoints) on which you want to install protection.
-
Click the
 Tasks button at the upper side of the table and choose Install .
Tasks button at the upper side of the table and choose Install .The Install Client wizard is displayed.

-
Under Options section, configure the installation time:
-
Now , to launch the deployment immediately.
-
Scheduled , to set up the deployment recurrence interval. In this case, select the time interval that you want (hourly, daily or weekly) and configure it according to your needs.
For example, when certain operations are required on the target machine before installing the client (such as uninstalling other software and restarting the OS), you can schedule the deployment task to run every 2 hours. The task will start on each target machine every 2 hours until the deployment is successful.
-
-
If you want target endpoints to automatically restart for completing the installation, select Automatically reboot (if needed) .
-
Under the Credentials Manager section, specify the administrative credentials required for remote authentication on target endpoints. You can add the credentials by entering the user and password for each target operating system.
To add the required OS credentials:
-
Enter the user name and password of an administrator account in the corresponding fields from the table header.
If computers are in a domain, it suffices to enter the credentials of the domain administrator.
Use Windows conventions when entering the name of a user account:
-
For Active Directory machines use these syntaxes:
username@domain.comanddomain\username. To make sure that entered credentials will work, add them in both forms (username@domain.comanddomain\username). -
For Workgroup machines, it suffices to enter only the user name, without the workgroup name.
Optionally, you can add a description that will help you identify each account more easily.
-
-
Enter the user name of an administrator account in the corresponding fields from the table header.
Use Windows conventions when entering the name of a domain user account, for example,
user@domain.comordomain\user. To make sure that entered credentials will work, add them in both forms (user@domain.comanddomain\user).Note
If computers are in a domain, it suffices to enter the credentials of the domain administrator.
Use Windows conventions when entering the name of a domain user account, for example,
user@domain.comordomain\user. To make sure that entered credentials will work, add them in both forms (user@domain.comanddomain\user). -
Select the authentication type from the menu:
-
Password , to use the administrator's password.
-
Upload .pem file , to use a private key.
-
-
If you authenticate using a password, enter the password in the field next to the menu.
-
If you authenticate using a private key, click the Browse button and select the
.pemfile containing the corresponding private key. -
Optionally, you can add a description that will help you identify each account more easily.
-
Click the
 Add button. The account is added to the list of credentials.
Add button. The account is added to the list of credentials.Specified credentials are automatically saved to your Credentials Manager so that you do not have to enter them the next time. To access the Credentials Manager, just point to your username in the upper-right corner of the console.
Important
If the provided credentials are invalid, the client deployment will fail on the corresponding endpoints. Make sure to update the entered OS credentials in the Credentials Manager when these are changed on the target endpoints.
-
-
Select the check boxes corresponding to the accounts you want to use.
A warning message is displayed as long as you have not selected any credentials. This step is mandatory to remotely install the security agent on endpoints.
-
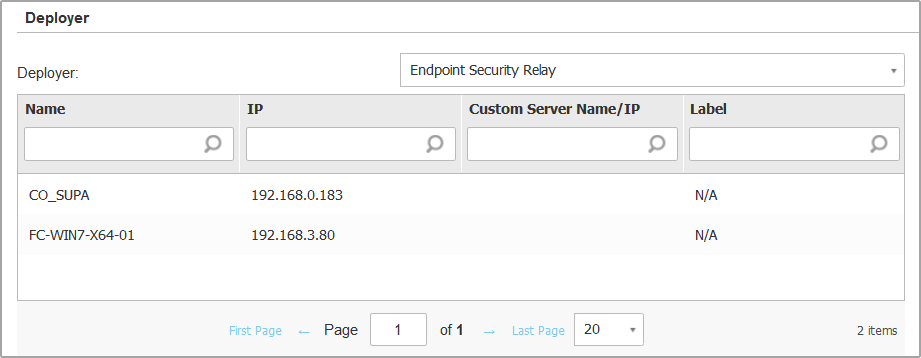
Under Deployer section, configure the Relay to which the target endpoints will connect for installing and updating the client:
-
All machines with Relay role detected in your network will show-up in the table available under the Deployer section. Each new client must be connected to at least one Relay client from the same network, that will serve as communication and update server. Select the Relay that you want to link with the target endpoints. Connected endpoints will communicate with Control Center only via the specified Relay.
Important
Port 7074 must be open, for the deployment through the Relay agent to work.
-
If target endpoints communicate with the Relay agent via proxy, you also need to define the proxy settings. In this case, select Use proxy for communication and enter the required proxy settings in the fields below.
-
-
You need to select one installation package for the current deployment. Click the Use package list and select the installation package that you want. You can find here all the installation packages previously created for your account and also the default installation package available with Control Center.
-
If needed, you can modify some of the selected installation package's settings by clicking the button Customize next to the Use package field.
The installation package's settings will appear below and you can make the changes that you need. To find out more about editing installation packages, refer to Creating Installation Packages.
If you want to save the modifications as a new package, select the Save as package option placed at the bottom of the package settings list, and enter a name for the new installation package.
-
Click Save .
A confirmation message will appear.
You can view and manage the task in the Network > Tasks page.
If using VMware Horizon View Persona Management, it is recommended to configure Active Directory Group Policy to exclude the following Bitdefender processes (without the full path):
-
bdredline.exe -
epag.exe -
epconsole.exe -
epintegrationservice.exe -
epprotectedservice.exe -
epsecurityservice.exe -
epupdateservice.exe -
epupdateserver.exe
These exclusions must apply as long as the security agent runs on endpoint. For details, refer to this VMware Horizon documentation page.
Uninstall client
To remotely uninstall the Bitdefender protection:
-
Go to the Network page.
-
Select the container that you want from the left-side pane. All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check boxes of endpoints from which you want uninstall the Bitdefender security agent.
-
Click the
 Tasks button at the upper side of the table and choose Uninstall client .
Tasks button at the upper side of the table and choose Uninstall client . -
A configuration window is displayed, allowing you to opt for keeping the quarantined items on the client machine.
-
Click Save to create the task. A confirmation message will appear.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Note
If you want to reinstall protection, be sure to restart the computer first.
Update client
Check the status of managed computers periodically. If you notice a computer with security issues, click its name to display the Information page. For more information, refer to Checking the endpoint status .
Outdated clients or outdated security content represent security issues. In these cases, you should run an update on the corresponding computer. This task can be done locally from the computer, or remotely from Control Center.
To remotely update the client and the security content on managed computers:
-
Go to the Network page.
-
Select the container that you want from the left-side pane. All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check boxes of endpoints where you want to run a client update.
-
Click the
 Tasks button at the upper side of the table and choose Update . A configuration window will appear.
Tasks button at the upper side of the table and choose Update . A configuration window will appear. -
You can choose to update only the product, only the security content or both.
-
Click Update to run the task. A confirmation message will appear.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Reconfigure client
The security agent's protection modules, roles and scanning modes are initially configured within the installation package. After you have installed the security agent in your network, you can anytime change the initial settings by sending a Reconfigure client remote task to the managed endpoints you are interested in.
Warning
The Reconfigure client task overwrites all installation settings and none of the initial settings is kept. While using this task, make sure to reconfigure all the installation settings for the target endpoints.
You can change the installation settings from the Network area or from the Endpoint Modules Status report.
To change the installation settings for one or several endpoints:
-
Go to the Network page.
-
Select the group that you want from the left-side pane. All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check boxes of endpoints for which you want to change the installation settings.
-
Click the
 Tasks button at the upper side of the table and choose Reconfigure client .
Tasks button at the upper side of the table and choose Reconfigure client .Note
Reconfigure Client page will not show which modules are currently installed on the endpoint.
-
Select one of the actions below:
-
Add - Add new modules besides the existing ones.
-
Remove - Remove specific modules from the existing ones.
-
Match list - Match the modules installed with your selection.
-
-
Under the General section, configure the time when the task will run:
-
Now , to launch the task immediately.
-
Scheduled , to set up the task recurrence interval. In this case, select the time interval that you want (hourly, daily or weekly) and configure it according to your needs.
For example, when other important processes are also required to run on the target machine, you can schedule the task to run every 2 hours. The task will start on each target machine every 2 hours until it is successfully done.
-
-
Configure the modules, roles and scan modes for the target endpoint as you want. For more information, refer to Install security agents - standard procedure
Note
You can only modify scan modes by using the Match list action.
Warning
-
Only the supported modules for each operating system will be installed.
-
The Firewall module is available only for supported Windows workstations.
-
-
Click Save . A confirmation message will appear.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Note
To successfully isolate the faulty endpoint module, uninstall each module individually and, after each removal, check if you can reproduce the issue.
Repair client
Use the Repair client task as an initial troubleshooting task for any number of endpoint issues. The task downloads the latest install package on the target endpoint and then performs a reinstall of the agent.
Note
-
The modules currently configured on the agent will not be changed.
-
The repair task will reset the security agent to the current Slow Ring version.
To send a Repair client task to the client:
-
Go to the Network page.
-
Select the container that you want from the left-side pane.
All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check boxes of endpoints where you want to run a client repair.
-
Click the
 Tasks button and choose Repair client .
Tasks button and choose Repair client .A confirmation window will appear.
-
Select the I understand and agree check box and click the Save button to run the task.
Note
To finish the repair task, a client restart might be required.
You can view and manage the task on the Network > Tasks page. For more, information refer to Viewing and managing tasks.
Restart machine
You can choose to remotely restart managed endpoints.
Note
Check the Network > Tasks page before restarting certain endpoints. Previously created tasks may still be processing on target endpoints.
-
Go to the Network page.
-
Select the container that you want from the left-side pane. All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check boxes of endpoints you want to restart.
-
Click the
 Tasks button at the upper side of the table and choose Restart machine .
Tasks button at the upper side of the table and choose Restart machine . -
Choose the restart schedule option:
-
Select Restart now to restart endpoints immediately.
-
Select Restart on and use the fields below to schedule the restart at the desired date and time.
-
-
Click Save . A confirmation message will appear.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Network discovery
Network discovery is automatically done hourly by security agents with Relay role. However, you can manually run network discovery task from Control Center at any time, starting from any machine protected by Bitdefender Endpoint Security Tools.
To run a network discovery task in your network:
-
Go to the Network page.
-
Select the container that you want from the left-side pane. All endpoints from the selected container are displayed in the right-side pane table.
-
Select the check box of the relay endpoint you want to perform network discovery with.
-
Click the
 Tasks button at the upper side of the table and choose Network discovery .
Tasks button at the upper side of the table and choose Network discovery . -
A confirmation message will appear. Click Yes .
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and managing tasks.
Update Security Server
You can install a Security Server appliance only by downloading the Security Server installation package to a network share or to the local host and deploying it manually on the host. Once installed, the Security Server will appear under the Custom Groups folder belonging to its network.
You can view Security Server details by clicking it and displaying the Information window. For details regarding the Security Server appliance installation, refer to this section.
If a Security Server is outdated, you can send it an update task:
-
Go to the Network page.
-
Select the group where the Security Server is installed.
To easily locate the Security Server, you can use the Filters menu as follows:
-
Go to Security tab and select Security Servers only.
-
Go to Depth tab and select All items recursively .
-
-
Click the
 Tasks button at the upper side of the table and choose Update Security Server .
Tasks button at the upper side of the table and choose Update Security Server . -
You will have to confirm your action. Click Yes to create the task.
You can view and manage the task on the Network > Tasks page. For more information, refer to Viewing and Managing Tasks.
How to Install Symantec Endpoint Protection Client on Mac
Source: https://www.bitdefender.com/support/troubleshooting-endpoint-protection-with-the-reconfigure-client-task-1905.html